In a garish brown blazer and with his youthful face, Park Jin Hyuk could pass as a teenager, stuffed into formal attire for a family occasion.
The truth is less benign. The only known picture of Park appears on the FBI’s most wanted list, where he is accused of being part of the state-sponsored North Korean cyber-attack that hacked Sony Pictures’ systems in 2014, in response to The Interview, a Sony-funded movie about the fictional assassination of North Korean leader Kim Jong-un.
Park is now thought to be a key operative in APT38, an aggressive and destructive North Korean hacking group that has used the Swift network to steal millions of dollars from banks worldwide, and which is now considered to be the highest-profile cyber threat to trade finance banks around the world.
Allegedly a North Korean computer programmer, Park is accused of participating in “a wide-ranging criminal conspiracy undertaken by a group of hackers” under the guise of a front company called Chosun Expo, which was operating in China.
Various social media profiles and email accounts belonging to Park have been tied to spear phishing operations emanating out of North Korea.
“Park Jin Hyuk is literally the only face we have for any of these operations. But he’s not the only one: the sheer scale of these operations of APT38 and associated groups indicate a very large operation, a full-on conspiracy. He just happened to be the one individual the FBI and other Department of Justice investigators can find enough info on to pin him to the group,” says Fred Plan, senior analyst in intelligence security company FireEye’s cyber espionage team.
FireEye has credited APT38 with cyber heists from Bangladesh to Chile, and from Vietnam to Mexico. Often groups of hackers are financially motivated, hoping only to line their own pockets. Sometimes, as is often the case in China, Iran and Russia, they’re state-sponsored, motivated to steal information or intellectual property, or as in many recent cases, to interfere in the affairs of other countries.
Along with other Pyongyang-directed groups, APT38 is in the usual position of being a state-backed actor, motivated by financial gain. Frozen out of international trade, a pariah state in almost every sense of the word, North Korea is desperate for income. Along with other illicit activities, such as selling chemical weapons to the Syrian regime and exporting methamphetamine around the world, cyber heists are a way for the regime to make money.
“It’s almost uniquely North Korean, that a nation state has stooped to conducting bank robberies using cyber,” Plan tells GTR. “There are other nation states out there that have the know-how or knowledge to do this, but because they’re embraced members of the international community they would not take action like this. But APT38 is in a weird overlap of being a group with the will and capability to conduct these operations. North Korea is in this outcast situation and it’s both motivated and has the capability.”
In the publicly-reported cyber heists alone, APT38 has attempted to steal US$1.1bn from financial institutions, often by exposing weaknesses in their internal systems, and subsequently gaining access to the Swift messaging network, through which it can transfer funds to an APT38-linked bank account.
FireEye has identified attacks on 16 organisations across 13 countries over the past four years. Among these is the 2016 hack on the Central Bank of Bangladesh, through which thieves stole US$81mn, by transferring cash to bank accounts in the Philippines. But for a typo in another outbound message, the hackers would have stolen US$850bn.
In the same year, Tien Phong Bank (TP Bank) in Vietnam was almost robbed of US$1mn due to fraudulent Swift messages, but in this case the bank was able to put a block on the heist. Hackers had gained entry to TP Bank’s systems using an outside vendor, which had been hired to connect it to the Swift network.
There’s no suggestion that Swift is at fault here: its system is targeted because it is so widely used. If there was another system used as widely, APT38 would likely be trying to break into it too. The fault is often down to lax systems on the part of users, or human error. Swift has refused to publicly comment on this report to GTR, declining to say how frequently its users’ systems are hacked.
“Slow burning espionage”
Most of the known target banks of APT38 hackers are in emerging markets. Attacks started out in Southeast Asia – Malaysia, Bangladesh, the Philippines, Vietnam, Taiwan – but have progressively broadened in geographic scope to Turkey, Brazil, Chile, Mexico, and even the US.
On studying the malware used by the hackers, FireEye suggests that a country’s developmental status may not act as a protection for its banks from this group.
“We’ve not yet seen them targeting banks that tend to have a very global reach, the big name banks. However, we’ve identified in their malware some strands that show they’re interested in targeting bigger banks that are cross-regional. Although to date all of the successful heists have been against banks in developing markets,” Plan says.
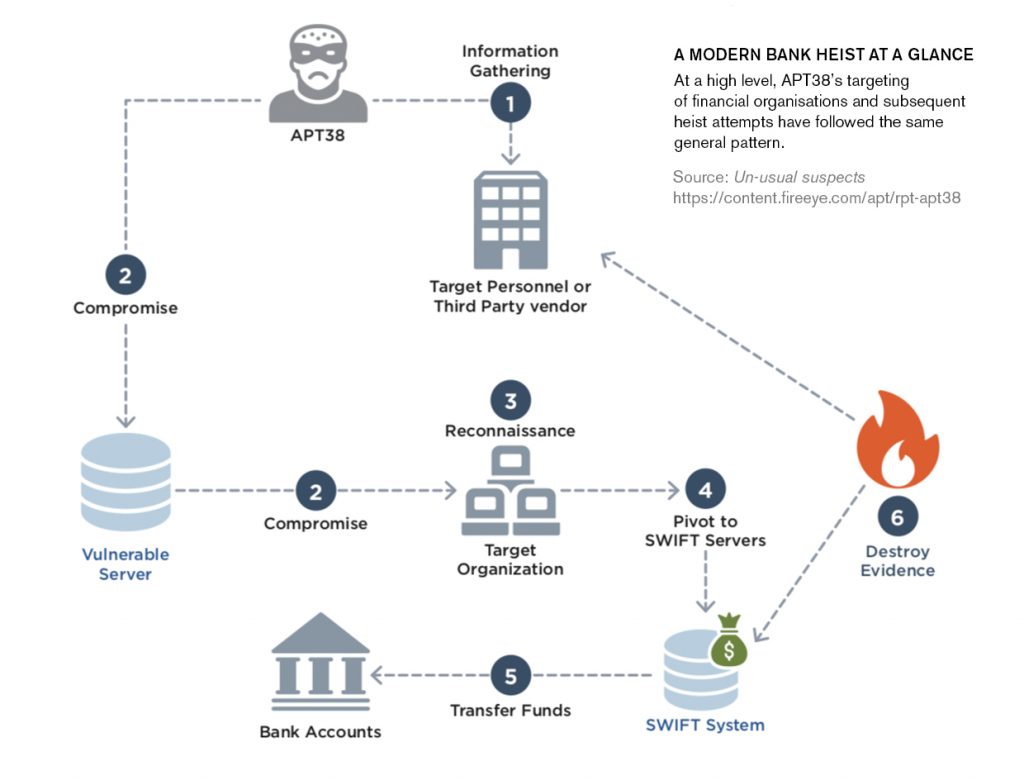
Generally speaking, these are not typical smash and grab-type heists. They are described as “slow-burning espionage”. Hackers begin with information gathering and reconnaissance, collecting enough information on a bank’s operations so that it can be designated as a target.
They will focus on scoping out potential weaknesses, often through an individual employee, or through the use of a third-party vendor. Once the group has access to the systems, they slow crawl their way through, identifying vulnerable servers, with the primary objective of gaining a deep understanding of how a bank does its day-to-day operations.
“They try very hard to identify specific individuals with access to accounts or systems until they have enough information, so that they feel they can pivot over to the Swift servers,” Plan says.
At this point, further reconnaissance takes place, identifying how the bank uses Swift, looking at the processes it uses to make payments, which computers they can leverage, and which tools they can use to manipulate transactions in a way that will prevent them from getting caught.
Each bank is different and so the operations tend to be highly-customised, played out over months or even years. The hacking tools and malware will be customised to target each financial institution.
Once they’re ready to start a heist, APT38 uses a malware set dubbed Dyepack by FireEye, a suite of tools that manipulates local data from Swift servers. Unlike clunkier, transposable malware used by other hacking groups, this is specifically designed to tackle the intricate nature of trade transactions.
Dyepack is used to make many, typically very large, fraudulent transactions to bank accounts usually set up in a different country. After this, the cash can be withdrawn overseas, before a series of money laundering activities helps wash the money, before it disappears.
In the Bangladesh Bank case, funds were sent to four banks accounts in the Philippines and one in Sri Lanka. Two individuals laundered tens of millions of dollars in an illegal gambling spree. The thieves waited for a bank holiday weekend in these countries before making withdrawals, in an effort to confuse things even more.
Simultaneously, APT38 uses wiper malware to cover its tracks further still. This destroys records of fraudulent transactions, often even leaving the bank’s systems unusable. The chaos in the systems also acts as a distraction in itself, making it easier to make off with the cash.
Attacks have become more sophisticated, devastating and efficient, Plan says. “The earliest ones weren’t nearly as destructive and often took longer – up to two years in some cases. Whereas the latter ones were faster and more willing to destroy systems and render them completely inoperable,” he explains.
What’s more, the lucrative nature of these heists has undoubtedly encouraged Pyongyang to keep them going. Even 15 years ago, Wired magazine reported on the hacking programme at Mirim College in North Korea’s mountainous North, billed “North Korea’s school for hackers”.
Now, Plan says, “there’s a very big pipeline of North Korean hackers that go through North Korea’s top universities, immediately recruited into the military”.
The cyber-elite unit is run out of Bureau 121, a North Korean department that has taken on near-mystical status in the online hacking community. The more North Korea is ostracised from the international trade network, the further it will delve into illicit activity such as this.
What was once thought as a peripheral threat has gained more sinister status. The near shave of the Bank of Bangladesh, where it almost lost US$1bn to APT38, via the Federal Reserve Bank of New York – custodian to much of the world’s gold reserves – has left cyber experts convinced that this is the most potent threat to trade finance banks online today.
One of the chief drivers of the industry’s digital revolution has been rampant fraud. Blockchain and AI may go some way to alleviating this, but they’re not perfect (Interpol warned in 2015 that blockchain could be repurposed as a means for spreading malware). You can bet that groups such as APT38, armed with a conveyer belt of specialists such as Park Jin Hyuk, are already working on cracking these technologies, even before they’ve fully taken off.